Good Facts On Deciding On Credit Card Apps
Wiki Article
What Can I Do To Determine The Authenticity Of A Credit-Card That Was Reported As Stolen In America?
Take these steps if you are interested in knowing if the credit card that you have used has been reported stolen or lost in the United States: Contact your Credit Card Issuer
Contact customer service at the number that is located on the reverse of the credit card.
The representative can be asked to confirm the status of the card.
Verification might require you to provide personal information, such as your credit card number as well as name.
Log in to your account
Log in to the online banking system or account associated with your credit card.
Be sure to check for alerts or messages regarding the condition of your credit card.
Review your transactions to identify suspicious or unauthorised transactions.
Check Your Credit Report-
Obtain a free copy of your credit report from each of the three major credit bureaus (Equifax, Experian, TransUnion) through AnnualCreditReport.com.
You should look over your credit reports for any suspicious inquiries or unidentified credit accounts.
Security Freezes, Fraud Alerts and Other Measures
If you suspect identity theft or fraud then place a fraud freeze or alert on your credit report.
A fraud alert will inform creditors that they need to make extra efforts to verify your identity prior to extending credit. However an order to freeze your credit report will restrict access to the credit report.
Keep an eye on the situation and report any suspicious Activity
Check your bank statements for credit card transactions. Notify the credit card company in the event of suspicious or unauthorized transactions.
Make sure you report any suspicious incidents for investigation to the Federal Trade Commission. You could also file a claim at your local law enforcement agency.
Contacting the issuer of your credit cards, reviewing the account activity on your website, monitoring your credit report and watching for any indicators of suspicious activities, proactive steps can be taken to protect you against credit fraud and resolve any potential issues relating to stolen credit.

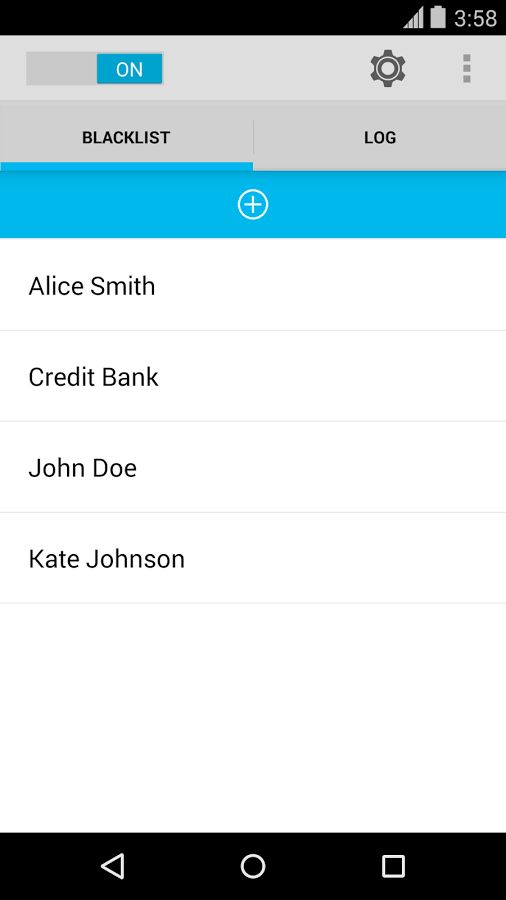
What Does It Mean That My Credit Card Is On A "Blacklist"?
A credit card placed on"a "blacklist" is one that has been flagged by the issuer, financial institution, or both due to the possibility of fraud, security concerns or other possible dangers. There are a variety of reasons why a card might be placed on a blacklist.
The suspicion of fraud - Blocking cards for security could be initiated by suspicious or unusual transactions which can trigger fraud detection software.
Security IssuesIn the event of signs of possible breach for example, unauthorised access, security breach involving the card's information or a pattern of spending that is unusual The card may be considered a security risk.
Identity Verification Problems- Issues that require verification of the identity of the cardholder during transactions could result in temporary blocking of the card, in particular when an additional verification is required.
Lost or Stolen Card- If the card has been reported stolen or lost by the cardholder, the issuer might apply a block to the card to stop the card from being used in a way that is not authorized until a replacement card is issued.
Suspicious Activity Indicatesthe presence of any behavior or activity related to your credit card that is suspicious, such as multiple declined transaction, geographical abnormalities, or unusual spending patterns could cause a temporary blockage.
When a credit or debit card is listed, it may restrict the cardholder’s access to the card or their ability to conduct transactions until the issuer of the credit card verifies its legitimacy, or resolves any concerns related to possible fraud or security risk. Cardholders must immediately contact their card issuer to report the problem and to verify the transactions and to resolve any security concerns.

How Do Cybersecurity Experts Monitor Cyber Threats And Identify The Stolen Credit Card Data?
Cybersecurity professionals utilize various methods, tools and methods to monitor and spot cyber-threats, such as compromised information on credit cards. The most common methods and practices are: Threat Intelligence Gathering
It is crucial to gather data from multiple sources, such as threat intelligence feeds (such as forums), dark web monitoring, and security alerts to keep up-to-date with new security threats and weaknesses.
Network Monitoring and Intrusion Detection
Use software designed for monitoring network traffic, and spot anomalies and suspicious activity that could indicate an unauthorised access to data or breach of.
Testing for vulnerability and penetrationTesting for vulnerability and penetration
Conducting periodic assessments to discover weaknesses within systems, applications or networks. Testing penetration tests mimic attacks in order to detect vulnerabilities and assess an organization's security posture.
Security Information and Event Management, (SIEM),
Implementing SIEMs that aggregate log data and analyse it across different sources (such a firewalls servers and applications) in order to identify security issues and react to them quickly.
Behavioral analytics -
Utilize behavioral analysis to identify irregular patterns or variations in user behavior, within networks or in systems. This could be a sign of an underlying vulnerability.
The threat of Hunting
Analyzing logs, system data and other data to identify potential threats which may have evaded the conventional security methods.
Endpoint Security Solutions-
Protection of systems and devices from malicious activity by deploying endpoint security tools including antivirus, antimalware, and endpoint detector and response (EDR) tools.
Data encryption and data protection
To minimize the risk of data breaches, use encryption techniques for sensitive data like credit card numbers, both during transit and while at rest.
In the event of an incident, we can assist with Forensics and Incident Response
Plan and implement strategies for incident response that allow you to respond promptly to security incidents. Conducting forensics to investigate, understand the consequences and quantify them of security breach.
Cybersecurity experts blend these methods with a thorough knowledge of changing cyber-security threats, compliance requirements and the most effective techniques to detect ways to mitigate and deal with cyber threats, such as those that involve compromised credit card information. Continuous monitoring, threat intelligence and a proactive security posture are critical in maintaining the security of your business against cyber-attacks. Take a look at the most popular savastano cc for site examples.